Many organizations start with basic MSP tiers: monitoring, backups, ticketing. These services work well initially, but they often become operational bottlenecks as systems scale, cloud adoption accelerates, and regulatory requirements tighten.
The gap between what basic MSP tiers deliver and what modern enterprises actually need creates measurable business risk. SLA breaches multiply. Security incidents take longer to detect. Internal teams compensate for MSP limitations by building shadow IT or spending excessive time on tasks the MSP should handle.
The solution requires understanding where your current MSP sits on the maturity spectrum and whether that positioning still serves your business objectives. A maturity model provides that diagnostic framework. It maps MSP capabilities to business outcomes and reveals when you have outgrown your current tier.
DBiz.ai's standardized, high-tier service catalogue addresses these gaps through AIOps integration, governance frameworks, and SLA protection engineered into every service layer.
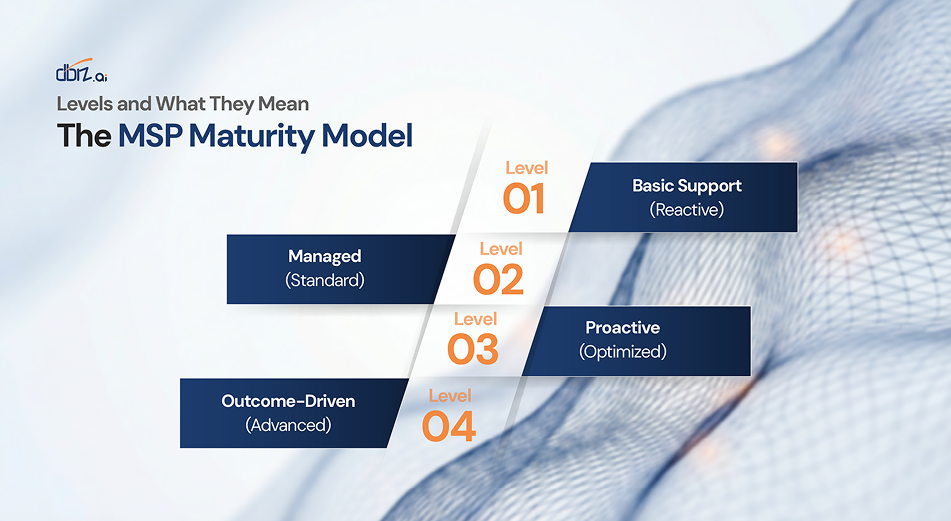
The MSP Maturity Model: Levels and What They Mean
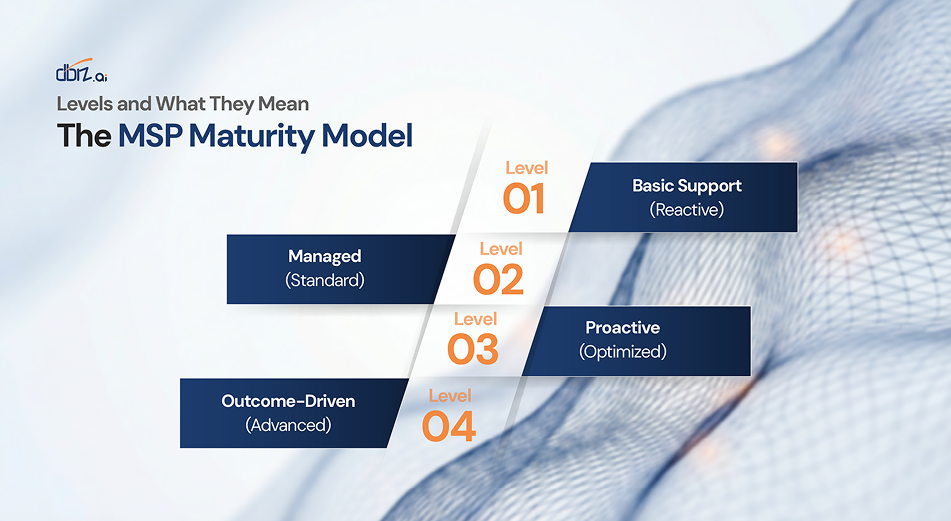
MSP maturity exists on a spectrum. Understanding where your provider operates helps you assess whether their capabilities match your operational complexity and risk tolerance.
Level 1: Basic Support (Reactive)
- Service characteristics: Break-fix ticketing, basic infrastructure monitoring, scheduled backups, helpdesk support. Response is entirely reactive. Monitoring alerts when thresholds breach, but provides no trend analysis or capacity planning.
- Typical SLAs: 4-hour response for critical issues, 8-hour for standard requests. No uptime guarantees. No proactive maintenance windows.
- Business limitations: High risk of unplanned downtime. No visibility into performance trends. Security monitoring is minimal or absent. Compliance documentation is manual and incomplete.
Level 2: Managed (Standard)
- Service characteristics: Defined SLAs with guaranteed response times, regular patching schedules, monthly maintenance windows, basic security monitoring, documented escalation procedures.
- Typical SLAs: 99% uptime commitment, 2-hour response for critical issues, quarterly business reviews. Predefined service catalogue with clear entitlements.
- Business limitations: Still largely reactive. Monitoring detects problems after they occur. Limited automation. No predictive capabilities. Alert correlation across tools is manual. Change management exists but lacks risk assessment.
Level 3: Proactive (Optimized)
- Service characteristics: Unified observability across infrastructure and applications, documented runbooks, automation for common tasks, integrated security monitoring, capacity planning, performance optimization, proactive patch management with risk scoring
- Typical SLAs: 99.5% uptime, incident avoidance targets, mean time to resolution commitments. Service catalogue includes automation playbooks and self-service options.
- Business limitations: Proactive but not predictive. Can identify issues faster but still reacts to events rather than preventing them. Business-impact prioritization is limited. Automation exists but coverage is inconsistent.
Level 4: Outcome-Driven (Advanced)
- Service characteristics: AIOps-powered predictive monitoring, business-aware SLA prioritization, capacity forecasting, change-risk assessment, safe automation with rollback capabilities, continuous compliance validation, strategic technology road mapping aligned to business outcomes.
- Typical SLAs: 99.9% uptime with SLA breach prevention metrics, incident avoidance KPIs, mean time to detect approaching zero for known patterns. Service catalogue includes outcome-based service definitions tied to business processes.
- Business impact: Incidents are prevented before customer impact. Security threats are detected through behavioral correlation across domains. Changes are gated by risk assessment. Automation handles routine scenarios safely while preserving governance. Service delivery aligns to business priorities rather than technical severity alone.
Most organizations start at Level 1 or 2. Growth, regulatory pressure, and customer expectations often drive requirements that these tiers cannot satisfy. Recognizing when that gap has widened enough to justify an upgrade protects both operational stability and business outcomes.
7 Signs You've Outgrown a Basic MSP Tier
Certain patterns indicate your current MSP tier no longer matches your operational needs:
Repeated SLA breaches or near-misses. Your monitoring detects issues, but too late to prevent customer impact or service degradation. Root cause analysis consistently reveals warning signs were present hours or days earlier but went unnoticed.
Lack of proactive monitoring or trend forecasting. Your MSP reports on what happened but provides no insight into what will happen. Capacity planning is reactive. You discover resource constraints through outages rather than advance warning.
Alert fatigue and no correlation across tools. Infrastructure, application, security, and cloud monitoring generate hundreds of alerts daily. No system correlates these signals. Critical incidents get lost in noise. Engineers spend more time managing alerts than resolving problems.
Security gaps or poor incident containment. Security monitoring exists in isolation. Threats that span infrastructure, applications, and user behavior go undetected because no correlation layer exists. Mean time to detect for sophisticated attacks measures in weeks or months rather than hours.
Slow change approvals with no CI/CD gating. Every change requires manual review and approval. No automated risk assessment. No testing in production-like environments. Change management creates bottlenecks that slow innovation while still allowing high-risk changes to reach production.
No service catalogue or unclear entitlements. Service definitions are vague. Response times are inconsistent. Teams disagree on what the MSP is responsible for versus what internal teams should handle. Budget conversations are contentious because scope and value are poorly defined.
Lack of strategic roadmapping or innovation partnership. The MSP executes tasks but provides no strategic guidance. Technology decisions are made in isolation. No alignment between MSP capabilities and business objectives. The relationship is transactional rather than collaborative.
Organizations experiencing multiple indicators typically benefit from upgrading to a higher maturity tier. The question becomes whether the business risk and operational friction justify the investment in enhanced capabilities.
DBiz.ai's outcome engineering approach starts by understanding which gaps create the most business exposure, then designs service upgrades that address those specific risks first.
Why Upgrading Matters: Business and Security Risks of Staying Put
Remaining on a basic MSP tier when your operational complexity has outgrown it creates measurable risks across multiple dimensions.
Business continuity risk increases. Reactive monitoring means incidents are detected after customers experience impact. For e-commerce platforms, every minute of degraded performance translates directly to abandoned transactions and lost revenue. For financial services, availability breaches trigger regulatory scrutiny and potential fines. For healthcare, downtime affects patient care delivery and creates liability exposure.
Security posture weakens. Fragmented monitoring creates detection gaps that sophisticated attackers exploit deliberately. A credential compromise in identity systems, followed by lateral movement through applications, followed by data access generates signals in three different monitoring domains. Basic MSP tiers lack the correlation capability to connect these events into a coherent attack narrative. Mean time to detect stretches from hours to weeks.
Compliance burden intensifies. Regulatory frameworks increasingly require continuous monitoring, automated controls validation, and complete audit trails. Manual compliance processes cannot scale. Basic MSP tiers provide incomplete logging, inconsistent retention, and fragmented evidence gathering. Audit preparation becomes a months-long exercise rather than a query against unified telemetry.
Operational costs rise. When MSP capabilities fall short of operational needs, internal teams compensate. Shadow IT emerges as teams deploy monitoring tools the MSP cannot provide. Engineers spend time on manual tasks that should be automated. On-call burden increases as incident volume grows. These hidden costs often exceed the investment required to upgrade to a higher MSP tier.
The managed services market continues growing because organizations recognize that operational complexity outpaces internal capacity. The differentiation now lies in whether MSP capabilities keep pace with that complexity or lag behind it.
The DBiz Standardized High-Tier: What Changes When You Move Up
DBiz.ai's advanced managed services tier addresses the limitations of basic MSP offerings through five integrated capabilities:
Standardized Service Catalogue with Clear SLAs: Every service has defined scope, ownership, response commitments, and success metrics. Entitlements are documented. Runbooks are versioned and accessible. Service requests have clear workflows. Escalation paths are automated based on business impact. The service catalogue provides transparency into what is delivered, how it is delivered, and how performance is measured.
Unified Telemetry Layer and Normalization: Logs, metrics, distributed traces, security events, cloud provider telemetry, and business KPIs flow into a centralized platform. Data normalization resolves timestamp inconsistencies, semantic differences, and format variations. The result is a complete operational graph showing relationships between infrastructure, applications, users, and business processes that fragmented tools cannot reveal.
Predictive AIOps Integration: Machine learning models analyze unified telemetry to identify patterns that precede incidents. AIOps capabilities include anomaly detection that understands contextual baselines, capacity forecasting that projects resource exhaustion weeks in advance, performance degradation prediction that alerts before customer impact occurs, and correlation engines that group related signals into coherent incidents.
The platform learns from every incident. Prediction accuracy improves continuously. False positive rates decline as models understand operational patterns specific to your environment.
Business-Aware Prioritization: Technical severity alone is a poor indicator of business impact. A database replica failure during low-traffic hours differs fundamentally from a payment gateway latency spike during peak sales. Business-aware prioritization maps technical events to revenue exposure, SLA risk, customer impact, and regulatory consequences. Incidents are scored and routed based on actual business priorities rather than generic severity classifications.
Safe Automation and Self-Healing Playbooks: For well-understood incident patterns with high confidence predictions, automated remediation executes without human intervention. Restarting degraded services, scaling constrained resources, clearing cache, rotating credentials. All actions execute within governance guardrails. High-risk operations require human approval. Lower-risk remediations proceed automatically but remain auditable and reversible. Automation coverage expands as confidence in predictions increases.
Governance and Compliance Integration: Audit trails are complete and tamper-evident. Change-risk assessment gates deployments based on historical incident correlation and current system state. Policy enforcement is continuous rather than point-in-time. Compliance validation runs automatically against defined controls. Evidence gathering for audits becomes a query rather than a manual collection exercise.
Outcome Reporting and Continuous Improvement: SLA dashboards visualize not just current health but projected risk based on trend analysis. Incident avoidance metrics track how many problems were prevented before customer impact. Periodic optimization reviews identify automation opportunities, performance improvements, and cost optimization. The MSP relationship evolves into a strategic partnership focused on measurable outcomes.
Implementation Path and Quick Wins: DBiz.ai typically begins with a focused pilot: select the top 3 business-critical services, establish telemetry ingestion and baseline learning, deploy two predictive alert models, implement one automated remediation playbook. This delivers measurable value within 90 days while building organizational confidence in the approach.
Target KPIs: reduce SLA breaches by 40-60% within 90 days, reduce alert noise by 70-80% through intelligent correlation, improve mean time to detect by 30%+ for covered services.
These capabilities represent what modern MSPs must deliver as operational complexity continues increasing and customer expectations for always-available, high-performance services become non-negotiable.
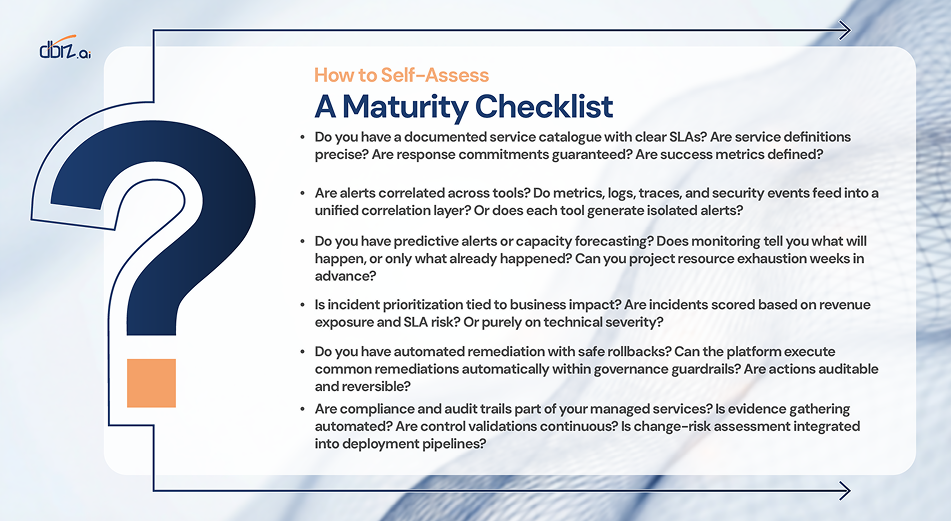
A Maturity Checklist: How to Self-Assess
Use this checklist to evaluate whether your current MSP tier matches your operational needs:
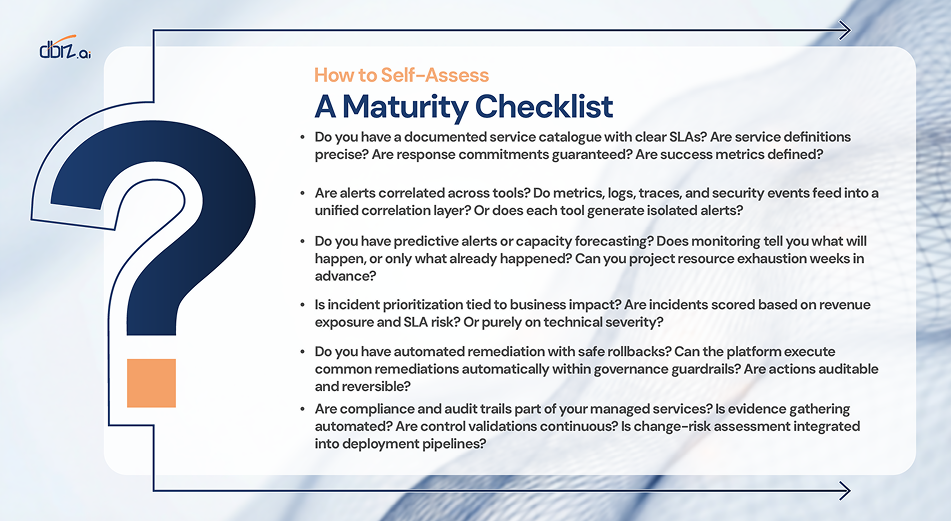
If you answered "no" to two or more items, your current MSP tier likely lacks capabilities that modern operational complexity demands. The business risk, security exposure, and operational friction justify evaluation of higher-tier services with AIOps integration.
Request a maturity assessment to understand where gaps exist and what upgrading would deliver for your specific environment.
When to Make the Move
Basic MSP tiers serve an important purpose. They provide operational support when internal capacity is limited and complexity is manageable. Growth, cloud adoption, regulatory pressure, and customer expectations often outpace these capabilities.
Use the maturity model and self-assessment checklist to determine whether your current MSP tier still serves your operational needs. The indicators are usually clear: repeated SLA issues, alert fatigue, security gaps, compliance challenges, lack of strategic guidance.
DBiz.ai's standardized high-tier service catalogue bundles AIOps, governance frameworks, and outcome reporting to reduce SLA breaches, strengthen security posture, and provide the operational intelligence that modern enterprises require.
Talk to DBiz.ai about a service catalogue-aligned maturity assessment and a 90-day AIOps pilot to standardize your managed services and protect your business outcomes.
Frequently Asked Questions
What is an MSP maturity model and why does it matter?
An MSP maturity model maps managed service capabilities to business outcomes across a spectrum of maturity levels. It matters because it provides a diagnostic framework for evaluating whether your current MSP tier matches your operational complexity and risk tolerance. Organizations often outgrow their initial MSP tier as systems scale, but lack a structured way to assess when capabilities fall short of needs. The maturity model makes that gap visible and quantifiable.
How do I know if I have outgrown my MSP?
Seven key indicators suggest you have outgrown your current MSP tier: repeated SLA breaches despite monitoring, lack of proactive trend forecasting, alert fatigue from uncorrelated tools, security gaps that delay threat detection, slow change processes without risk assessment, unclear service entitlements or missing service catalogue, and absence of strategic guidance or innovation partnership. If you recognize multiple patterns, your operational needs likely exceed current MSP capabilities.
What does a high-tier MSP with AIOps provide that basic tiers do not?
High-tier MSPs with AIOps deliver predictive capabilities rather than reactive response. This includes ML-based anomaly detection that identifies issues before customer impact, capacity forecasting weeks in advance, business-aware incident prioritization based on revenue and SLA exposure, automated remediation within governance frameworks, unified telemetry correlation across all monitoring domains, and continuous compliance validation. Basic tiers respond to problems after they occur. Advanced tiers prevent problems from occurring.
How quickly can DBiz reduce SLA breaches after upgrading?
DBiz.ai typically targets 40-60% reduction in SLA breaches within 90 days through focused pilots. The approach starts with top 3 business-critical services, establishes telemetry baseline learning, deploys predictive models for common incident patterns, and implements automated remediation for high-confidence scenarios. Speed depends on existing telemetry maturity and service complexity, but measurable improvement appears within the first 30-60 days as predictive models begin identifying degradation before it escalates.
What does a service catalogue-aligned migration look like?
A service catalogue-aligned migration begins with documenting current state: what services exist, what SLAs apply, where gaps exist between expectations and delivery. DBiz.ai then maps standardized service definitions to your business processes, establishes clear ownership and escalation paths, implements unified telemetry ingestion, deploys AIOps correlation and prediction, automates remediation for common scenarios, and establishes outcome reporting dashboards. The process is phased, starting with highest-impact services and expanding coverage based on demonstrated value.